Beginners' Guide to Privacy
Think of this as your roadmap for the privacy revolution: why the old ways didn't quite work for regular people and how the new wave is finally making Web3 safe for the rest of us
We’ll be covering 4 sections
2.1 Privacy as a Spectrum
2.2 The Evolution of Privacy (from 0.9 to 2.0)
2.3 Cryptography & Encryption
3.1 Supply of Privacy - Applications & Use Cases
3.2 Demand of Privacy - Where Demand is coming from
3.3 Privacy Ecosystem Map
4.1 Key Figures & Traction of Privacy Projects
4.2 Funding Options
For those who would like to see the visualized overview deck of this piece before diving in, feel free to check it →> HERE <←
1. Introduction to Privacy
Things in the physical world are private by default — banks don’t disclose your entire net worth to other customers when you use it.
Global regulations and data laws (like GDPR or HIPAA) enforce compliance, requiring businesses and individuals to comply, to keep data private.
Now contrast this with blockchain.
Blockchain is public by default, commerce happens in public — every transaction, balance, strategy, position is broadcasted to a global ledger, visible to anyone, forever.
Imagine you are iShowSpeed paying for a meal in Nigeria with a stablecoin. On a blockchain, someone can link that payment to your wallet. Suddenly, your entire net worth, your past purchases, and your current location are exposed to the world.
In the digital age, this kind of public crypto wallet is a physical target.
As blockchain and stablecoin adoption scale, privacy needs to evolve from a “nice-to-have” into a “must have” (GDPR, MiCA, AML required for large-scale commerce).
For Web3 to achieve mass utility, it must provide the same privacy safeguards that that we have in the physical world.
2. Privacy as a Product
2.1 Privacy is a Spectrum
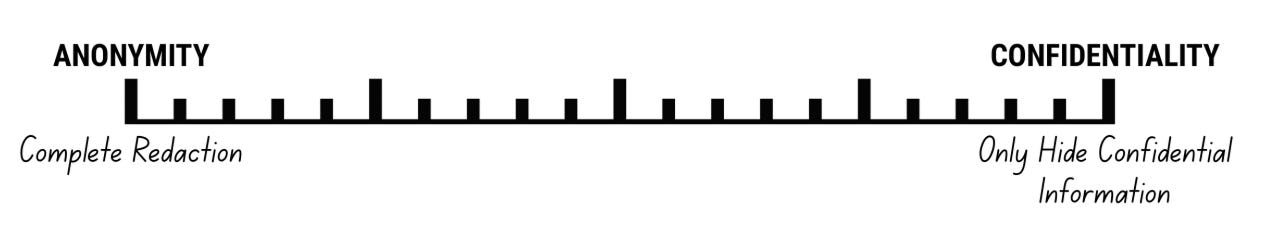
In Web3, “privacy” is often framed as a binary: either you’re fully transparent like Ethereum L1, or fully anonymous like early privacy chains like Monero or Zcash. But, the reality is not that binary.
Across chains and products, privacy is implemented as a spectrum of choices around who can see what, when, and under what conditions.
These choices determine the adoption, and therefore the success of those chains and products in the age of 24/7 global finance.
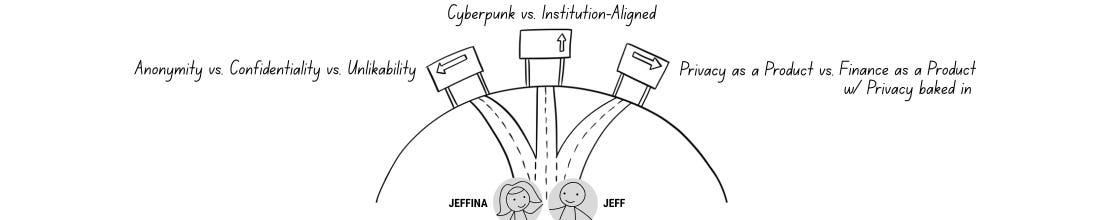
The Choice of Anonymity vs. Confidentiality vs. Unlinkability
The Choice of Cypherpunk vs. Institution-Aligned
The Choice of Privacy as a Product vs. Finance as a Product with Privacy baked in
The Choice of Anonymity vs. Confidentiality vs. Unlikability
Anonymity hides who you are, hides the action & the balances, and hides the person or the counterparty that you are transacting with.
Jeffina sends 100 USDC to Jeff. No one knows this except Jeffina and Jeff. Jeffina doesn't know the details & financial history of Jeff's wallet, and Jeff does not know Jeffina's. This is possible thanks to cryptography.
Classic privacy coins/shielded pools (Monero, Zcash) & mixers (Tornado Cash) fall into the Anonymity camp. They make sender, receiver, and balances completely anonymous.
Anonymity often faces regulatory pressure, delistings from centralized exchanges, and constraints in liquidity for transacting and bridging.
Confidentiality keeps sensitive data hidden, while keeping sender, receiver, or the counterparty public.
Jeffina sends 100 USDC to Jeff. Everyone knows that Jeffina sends USDC to Jeff but they don’t know how much USDC is being sent.
Most founders gravitate toward confidentiality-by-design with optional or role-based transparency, not absolute anonymity.
Confidentiality allows parties like regulators, counterparties, or apps to know enough to do business or stay compliant with regulations, data & privacy laws (MiCA, FATF, AMLR, GDPR, CCPA, and more)
Privacy 2.0 infra/protocols (using FHE/MPC + ZK) often fall into this camp. They prioritize having selective disclosure, sanction/freeze list features, to comply with rules & regulations. These features also allow them to monetize the tech to broader crowd outside of crypto (e.g. Privacy 2.0 tech powering fintech app in emerging markets — regulators can audit and check that they comply with data laws)
Unlinkability breaks the financial link of your existing wallet(s), allowing you to start fresh with a new wallet OR obfuscating activity on your existing wallet(s), making it harder for others to trace.
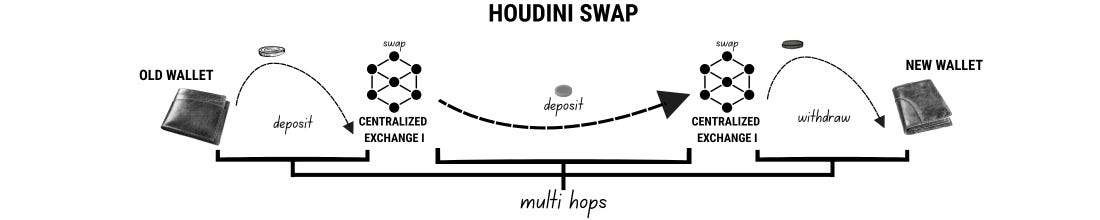
While anonymity (mixers & shielded pools) delivers the unlinkability property, there are privacy apps & tools that are designed primarily to break the link on your wallet without cryptography (e.g. Houdiniswap using CEXes + multi hops or Mirage using escrow smart contract to unlink your activity or send funds privately)
Why this matters: Understanding the difference between the form of privacy is key to understanding privacy product
The Choice of Cypherpunk vs. Institution-Aligned
Cypherpunk leans on maximal individual privacy - it’s the idea of staying completely anonymous, freely moving capital around without getting tracked, and having minimal institutional control.
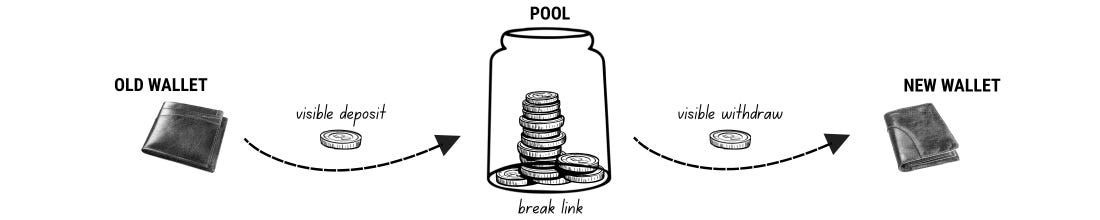
Privacy mixers like Tornado Cash and its forks are the best example of Cypherpunk ideology. Users deposit funds into the mixer, wait a few days for more people to deposit, and users withdraw. The longer the wait, the more the deposits, the harder it is for on-chain sleuths to track & find patterns.
While U.S. sanction on Tornado Cash was lifted in 2025, Tornado Cash users still get tagged as “Tornado Cash-linked wallets” every time they use Tornado Cash. Tagged users are denied access to many Defi protocols today.
Complete anonymity may just be the ideal setup that some people want but it’s certainly not what the institutions and enterprises are looking for.
Institution-aligned puts institutions and enterprises first - it’s the idea of keeping sensitive information confidential while complying to rules, regulations, and compliance.
Why this matters: Most founders are aligning with institutions and complying with rules and regulations.
Why? because the best privacy is the privacy that people use. That’s why.
The Choice of Privacy as a Product vs. Finance as a Product with Privacy baked in
I’ve talked to over 2 dozen privacy teams and what I’ve found is that — regardless of where they’re on the privacy spectrum, the most important choice is choosing between privacy as a product vs. finance as a product with privacy baked in.
Privacy as a product = selling a product/infra with privacy as the key feature.
Teams that execute well in this category are usually teams that sell privacy infrastructure with end use cases in mind OR they secure demand first (startups, enterprises, institutions) when building out the infrastructure.
Privacy is not limited to just financial use cases either, there are many use cases outside of crypto, it could be identity/ownership (KYC only once and use the shared identity across platforms), payments (using facial recognition/iris to pay for food), etc.
The sad thing I’ve noticed in web3 privacy is that many legacy privacy projects sell privacy as a product with shitty UI/UX. Clunky, unreliable experience while charging high fees to move capital around privately. There are stories of funds getting stuck for days to weeks because the infra is down.
Stories like this might be a thing in the past though, thanks to the renewed wave of privacy interest, pushing projects to think beyond web3, prioritize UI/UX, and embed privacy as the backbone infrastructure for the mass.
Why this matters: Trend is pointing towards practical implementation of privacy 2.0 infrastructure which will lead to bigger on-chain usage of privacy + unique privacy sub-segments like private defi, private trading, private prediction markets, and private ai.
Finance as a product with privacy baked in = selling finance as the main product with privacy as a backbone infrastructure.
A few teams that I’ve talked to opted to focus their time on the commercial side of things instead of spending years on cryptography research and coming out with best privacy guarantees (i.e. lowest risk of data getting exposed), they focus on working with fintech startups, neobanks, and traditional businesses to onboard businesses to blockchain rail, stablecoins, and Defi while using TEE to secure the privacy.
These fintech startups have recently started to look into adopting blockchain rails & stablecoins due to its cheap fees (no middlemen) + fast settlement (no T+2) but challenges remain on the privacy side of things.
TEE is used due to its flexibility & ease of implementation BUT it’s often referred to as the technique with lowest privacy guarantee (meaning the underlying data is easier to be exposed compared to other tech) but according to some people, this is already better than legacy system already when it comes to encrypting data or keeping data private.
[Will dive into cryptography, encryption, and privacy tech in a bit to provide more colors on this]
Why this matters: Another trend pointing towards potential acceleration in blockchain & stablecoin adoption. TEE itself is popularly used for any types of data (e.g. confidential computation and private inference keeping user prompts, AI computation, and its inference/outputs private)
2.2 The Evolution of Privacy (from 0.9 to 2.0)
Over the years, the way we try to fix blockchain’s “public by default” has changed a lot. We’ve gone from “clunky apps that make you look like a criminal” to “entire blockchains that are hard to use,” and finally to where we are now: Privacy 2.0, where privacy actually feels like a normal feature rather than a massive chore.
To understand why the new stuff is so cool, we have to look at the three “eras” of privacy and why the first two didn’t quite stick the landing for regular users.
Privacy 0.9: The Mixer Era (Application Layer)
Privacy 1.0: The Privacy Coin Era (Infrastructure Layer)
Privacy 2.0: The Programmable Era
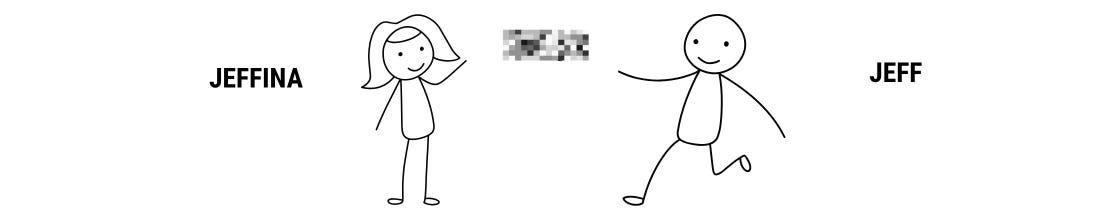
Privacy 0.9 is an application layer, which refers to mixers like Tornado Cash. The reason why it’s called mixers is because the way privacy works at a high level is
People send their assets (e.g. ETH) into the mixer pool
Your ETH gets mixed with other people’s ETH
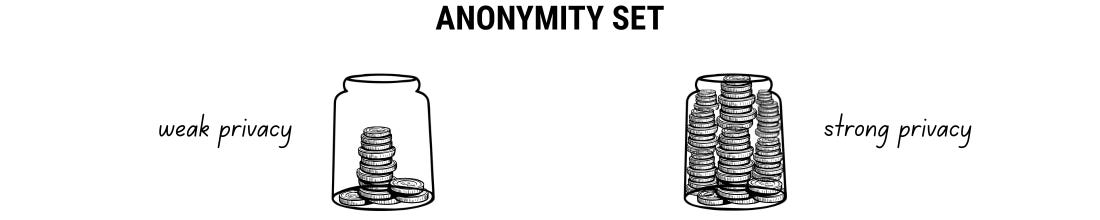
The longer your ETH sits in the pool, the better the anonymity set (the liquidity within the pool)
After 48 hrs (or however long you want to wait for), you withdraw your ETH to a new wallet
The link with your old wallet is now severed BUT.....
The downside to using a mixer is it’s prone to timing & pattern analysis. Since your ETH is visible when it’s going into the mixer pool as well as when it’s coming out of the pool, on-chain sleuths could potentially match the new wallet with your old one, linking the identity together.
What’s worse is.... even though Tornado Cash U.S. sanction was recently lifted in 2025, if you use it, your wallets get tagged with “Tornado Cash”. This could result in you not being able to interact with defi protocols or not being able to off-ramp with centralized exchanges.
Mixers serve the most basic privacy use case which is hiding the balances and cutting the on-chain traces. Unfortunately, mixers are often targeted by the regulators or governments as they are often used by scammers (e.g. Lazarus Group).
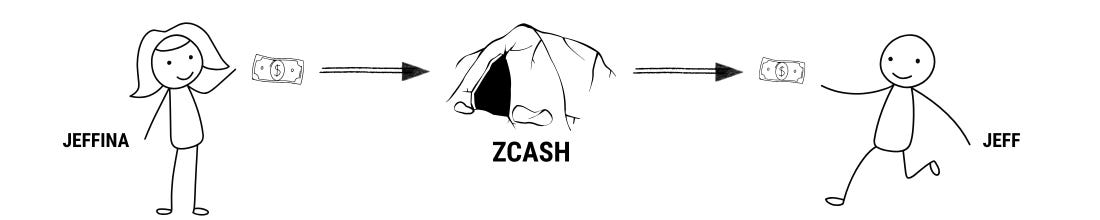
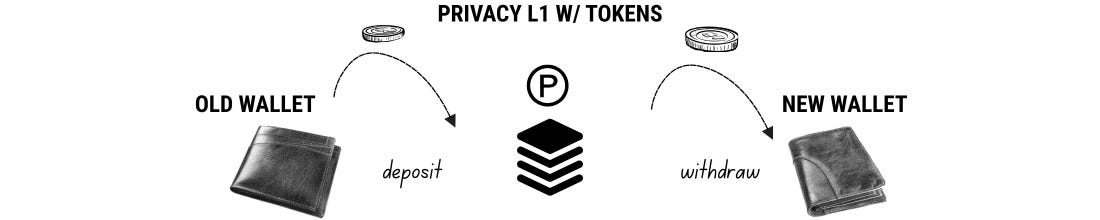
Privacy 1.0 serves a similar purpose to Privacy 0.9 BUT instead of application layer, it’s infrastructure layer.
This is private L1s designed for privacy within the network. Popular ones are Monero & Zcash, both also position their tokens as “medium of private payment“ or playing with the “Bitcoin of Privacy“ narrative.
From user POV, instead of just depositing funds into an app, you have to bridge your capital over to these separate networks to get any privacy
You’re forced to use their native tokens ($XMR or $ZEC) to do anything. This means you’re stuck dealing with their price volatility, and you can’t use stablecoins or other assets you actually want to hold.
While these private blockchains aren’t targeted as much by regulators as mixers are, they’ve been getting delisted from major exchanges for years. This makes it a massive pain to actually buy the tokens or get your money back into the real world.
Ultimately, both 0.9 and 1.0 are limited — they’re really only good for breaking a link or making private payments, and they usually require a lot of heavy lifting from the user to get it right
Privacy 2.0 takes this a step further, expanding privacy to more use cases with a much more seamless experience.
Instead of using altcoins as medium of exchange, Privacy 2.0 allows you to use stablecoins as the medium of exchange, avoiding volatility risk that comes with altcoins. Some projects even offer yields on top of stablecoins, allowing users to earn yields while holding the stablecoins.
Instead of having to bridge your funds to a separate L1s, Privacy 2.0 allows you to access confidentiality directly on EVM or on Solana.
Privacy 2.0 introduces “programmable privacy“ where the privacy can be embedded into logic, processes, smart contracts, applications, and computation in the existing chains & applications.
This enables use cases like private defi, private trading, darkpools, private ai, private prediction markets, private launchpads, private DAOs, and many more.
Disclaimer: I’m just loosely grouping next-gen privacy infra/products into Privacy 2.0 - not all protocols have the same features & properties. Some still require you to bridge your funds to their chains, some focus on use cases outside of crypto, some focus on cross-chain bridging, some focus on privacy on Solana, some on EVM, you get the idea.
[We’ll deep deeper into the nuances of this in a bit]
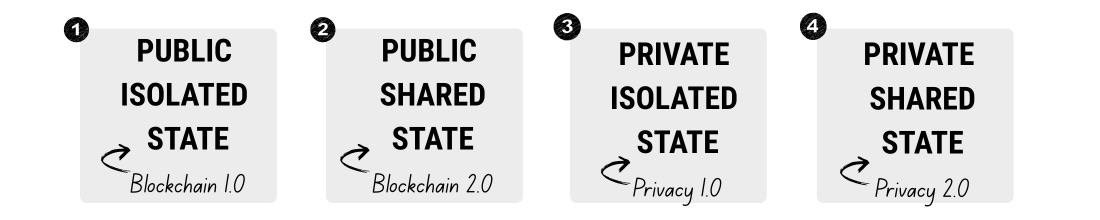
The 4 Stages of Digital State
The evolution of privacy can also be studied from the lens of digital state.
Where we move from digital cash (public isolated state) to world computer (public shared state) to private digital cash (private isolated state) to private world computer (private shared state)
Public isolated state: Bitcoin/Blockchain 1.0 era = Public Blockchain + No Smart Contract
Public shared state: Ethereum/Blockchain 2.0 era = Public Blockchain + Smart Contract & dApps
Private isolated state: Zcash/Privacy 1.0 era = Public Blockchain becomes Private + No Smart Contract
Private shared state: Privacy 2.0 era = Public Blockchain becomes Private + Smart Contract & dApps become Private
Bitcoin is Blockchain 1.0
Bitcoin was the 1st blockchain created in 2009 that's considered having a public isolated state
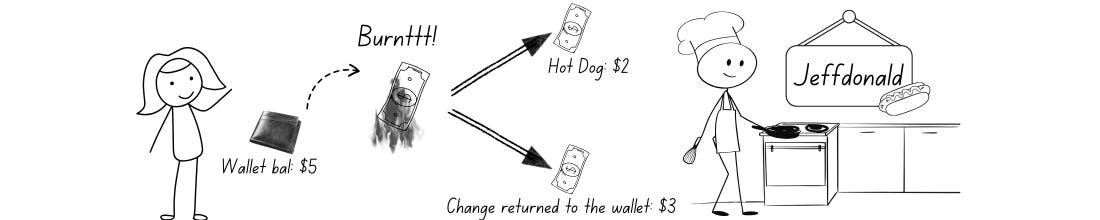
The Bitcoin UTXO model is structured like physical cash instead of a digital bank. You can have bills that represent 0.5 BTC, 1 BTC, 2 BTC with unique identifiers.
The state of each bill is separated from each other (think of this like a pile of cash) so when spending the bill and receiving change, the amount is always clear (previous bill burnt when spent, change returned to the wallet instead).
The benefit of public isolated state is that it’s secure BUT doesn’t allow for smart contracts & decentralized applications
Ethereum is Blockchain 2.0
Ethereum changes the game with an account-based model (similar to bank or Venmo) where it’s an address with a balance and the network just does math every time a transaction happens.
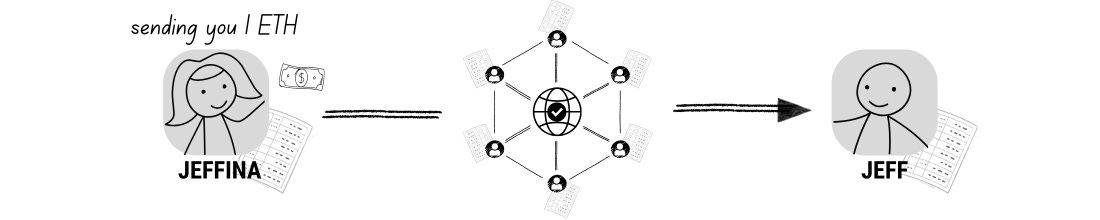
Jeffina sends 1 ETH to Jeff, the network verifies Jeffina’s total balance, subtracts 1 ETH plus gas fees from her account, and adds 1 ETH to Jeff’s account by updating a single global ledger. Everything is visible in public.
With account-based model, smart contracts are possible. This creates a shared state where things can interact with each other on-chain (e.g. Uniswap contract - funds like ETH/USDT pooled together, creating a public shared state). Smart contracts enabled the proliferation of defi innovations & on-chain ecosystems worth >$100B TVL and >$300B stablecoins today.
The benefit of public shared state is having the optimal environment for decentralized applications BUT since everything is public, there’s no privacy
From evolution POV, we moved from a public isolated state to a public shared state BUT challenges remain for broader institutional & enterprises adoption
Zcash is Privacy 1.0
The need for privacy gave rise to private isolated state (i.e. Zcash). Using Zcash as a canonical example, it’s fundamentally based on the Bitcoin UTXO model but with zero-knowledge proofs (ZK-SNARKs), creating a parallel “shielded” ledger.
Stay with me here.
Think of Zcash as a tunnel. Within that tunnel, there’s a separate mini dark tunnel. This mini dark tunnel is a shielded pool, and you can’t see anything in it. You can’t see who’s doing what, who’s transacting with who, how much is being transacted.
The downside here is that it’s a private isolated state/UTXO model — you can only use $ZEC to transact (send & receive ZEC) within the pool & there’s no decentralized application/no defi ecosystem within Zcash.
The benefit of private isolated state is that it’s secure & private (like Bitcoin but private) AND just like Bitcoin, there’s no smart contract & decentralized application
Enter Privacy 2.0
But accessing privacy like this is complicated & not optimal. Users are required to buy the token & bridge in order to access privacy (in this case it’s $ZEC and bridge to Zcash chain). There’s also no applications since it’s an isolated state so you can’t do much beyond sending & receiving the token privately.
This brings us to private shared state, using encryption/cryptography to make privacy programmable on public blockchains, turning public shared state private.
Commercial applications require verifiable data from multiple sources (e.g. KYC data, on-chain data, AI data, banking data, etc). Being able to verify these data + being able to compute on them while keeping the data encrypted is key in complying with rules & regulations.
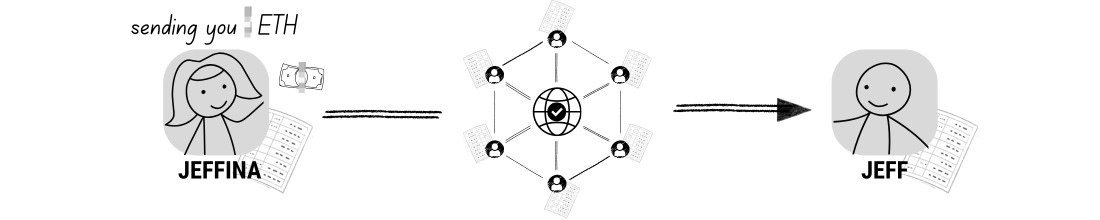
Jeffina sends 1 ETH to Jeff, and while the network verifies the balances and updates the global ledger, the transaction details are encrypted so that only Jeffina and Jeff see the amount and addresses, while the public only sees a cryptographic proof that the transfer was valid
Privacy 2.0 is all about compliance/data sovereignty (how data is collected, stored, who can see it, who owns it, etc) complying to local laws like GDPR.
If Robinhood allows other users to see your assets, transactions, and net worth, Robinhood would be in trouble (due to regulations). The same thing applies to on-chain applications.
On-chain apps are inherently transparent (due to the nature of blockchains) which makes it harder for on-chain apps to serve broader non-crypto consumers.
This will likely change soon as Privacy 2.0 continues to move blockchain from public shared state towards private shared state.
In order to make public state private & verifiable, cryptography & encryption are needed to make it possible.
2.3 Cryptography & Encryption
Verifiable privacy is built using the combination of cryptography & encryption(/decryption) which utilizes math & algo to secure data and information + turn data into scrambled/unreadable format.
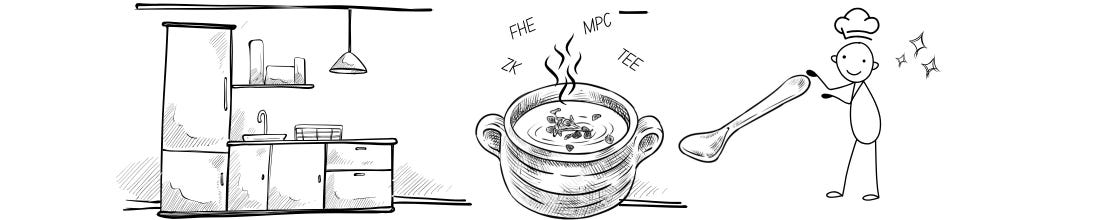
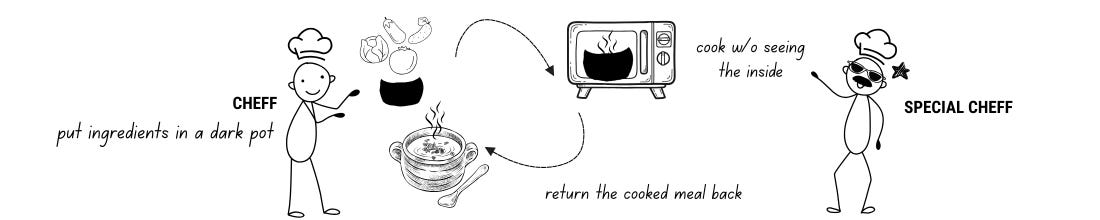
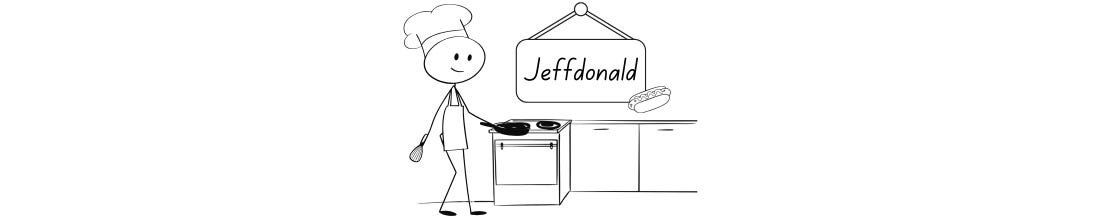
One of the best analogies for this might be a chef serving a meal to customers
The kitchen = the privacy infrastructure or chains providing tools to chefs
The chefs = devs/apps using the kitchen to cook
Methods of cooking = techniques like ZK, MPC, FHE (e.g. ZK can be combined w/ MPC)
Ingredients = different types of data (on-chain data, private keys, name, personal ID card, physical address)
The meals = end use cases (private transfer, payments, defi, ai)
Just as there is no single way to cook a meal, there is no 'one-size-fits-all' for privacy; protocols choose different cryptographic tools based on the specific complexity and sensitivity of the data they are processing.
Zero-knowledge proofs (ZKPs)
Most popular cryptography & most used in space. 70-80%+ of privacy projects utilize ZK in one form or another. It is best used to prove an individual state without sharing sensitive information.
ZK proof is like making a meal with a secret recipe. The chef cooks behind a closed curtain, no ingredients are shown to the customers. The finished plate is handed to the customers in the end.
The meal in this case is a private transfer or an identity verification.
The customers may want to know if the meal is nut-free. The chef doesn’t show them the ingredients or the pantry, the chef provides a Certified Lab Result (the ZK proof) that confirms “This meal contains no nuts” without revealing the secret ingredients.
ZK has seen 10-100x improvements in cost efficiency over the last 5 years, moving from theoretical towards practical, production-ready tool. Proving a transaction now takes seconds. All thanks to the improvements in ZK tech, hardware, and tooling.
Great for use cases like
Proving that you’re 18+ without disclosing the exact age (KYC)
Prove loan collateral without exposing your balance
Verify model execution without exposing your data
ZK alone is great at proving its own/individual state.
But if we were to create private applications involving interactions across multiple states (not just your data but others’ data like private DEX/LP’ing, private lending/borrowing), other techniques are needed to make shared private state possible
This is where MPC & FHE comes in
Multi-party Computation (MPC)
Second most popular cryptography. Over 10-15% of privacy projects utilize MPC to enable privacy 2.0 use cases.
MPC = Multiple parties jointly work (compute) on a task together.
Using the same analogy, MPC is like making a Potluck Kitchen. No single chef has the whole recipe.
Chef A has the cabbage, Chef B has the eggplant, Chef C has the tomato, and Chef D has the calabash.
They all stand around a pot in the dark.
Each chef tosses their “piece” into the pot and stir. No one knows exactly how many tomatoes Chef C put in, but the final meal (the “result”) is perfectly cooked.
The meal in this case is secure asset custody.
MPC is used by custody providers like Fireblocks so that the private key (of a client) never actually exists in one place. Instead, 3 different servers hold “shards” of the key. To sign a transaction, they perform MPC to generate a signature without ever reassembling the full key on any single machine.
The key challenge with MPC is chefs collusion
The risk of chefs colluding to put all the shares together to see the recipe. In high-stakes use cases like asset custody, the chefs (MPC servers) can collude to reconstruct their keys, get the private key, and drain the wallet.
There are guardrails in place to mitigate this risk such as using TEE, setting policies, picking the right chefs, etc.
Privacy 2.0 use cases are possible because MPC is combined with ZK
ZK to prove & verify individual state (private state)
MPC to jointly work on something without sharing secrets (shared state)
Together you get a system where no one sees the data and everyone can see the proof that the result is 100% accurate (shared private state)
This kind of system is optimal for use cases like darkpool/private trading where
MPC finds a match between your hidden buy and sell orders. Once matched,
ZK proves to the blockchain that the trade was valid (e.g. I actually had the 10 ETH I just sold).
Fully-Homomorphic Encryption (FHE)
FHE has recently become popular, thanks to the drastic improvement of FHE technology. Only a few privacy projects utilize FHE because the overhead cost is very very high.
FHE = You can compute on encrypted data directly without decrypting
The chef puts the ingredients in a dark (encrypted) bag. The chef then hands the dark bag to a specialized chef, who puts the bag in an industrial oven. The specialized chef hands the bag back to the chef as a cooked meal, all without seeing what’s inside.
The meal in this case is a confidential transfer, encrypted health score (healthcare), credit score (banking), etc.
FHE is considered to be the holy grail of privacy because the data can always stay in an encrypted state while computation is happening. It allows the banking and healthcare sectors to derive critical insights from sensitive datasets while maintaining end-to-end confidentiality and meeting strict regulatory standards.
The Problem with ZK + MPC
ZK is great for individual secret, but it struggles when everyone’s secrets are mixed in a pool. If the pool’s total balance is hidden, how can I prove my new deposit doesn’t break the pool’s math without seeing everyone else’s deposits?
MPC requires “Chefs” to be online to talk. If you want a permissionless lending pool where anyone can deposit at 3 AM, you can’t wait for a committee of MPC servers to wake up and coordinate.
FHE solves ZK + MPC problem (in theory)
FHE allows a smart contract to “live” in an encrypted state. It can automatically add your encrypted deposit to the pool’s encrypted total and calculate your interest—all while the numbers stay “in the locked bag”.
Example (Private lending/borrowing): You deposit 1,000 “Encrypted ETH” as collateral. The FHE contract calculates your “Encrypted Borrowing Power” and mints a loan for you. The world sees a transaction happen, but no one (not even the contract owner) knows the amounts.
Zama has recently shown a major FHE pilot involving ~$120M+ in capital with a sealed-bid auction community round. You (investor) hide your USDT, others see you hold a stablecoin without seeing the balance and without knowing how much you’re participating in the community round at what price).
In practice, the reason why FHE hasn’t really taken off is because of the speed & cost. The sheer processing power needed for encrypted math is significantly higher (>10,000x) than using ZK + MPC. Unless we see a breakthrough that can bring the costs down, we won’t see private lending/borrowing any time soon.
[Some teams are saying breakthroughs have already happened and we might see early pilots of this by end 2026 or 2027 though].
Trusted Execution Environment (TEE)
Many projects are building in TEE — they’re often sector agnostic because the tech is considered to be an add-on to cryptography.
TEE = Run code in a secure hardware enclave so even the machine’s OS / operator can’t see the code or data while it’s running.
TEE is like a locked prep station within the kitchen, making the cooking operation more secure & private. The ZK, MPC, FHE cooking operation can happen within TEE (in fact, this is a meta for modern privacy solutions).
TEE can easily be added to make whatever you do private. It can be quite customizable & doesn't require large overheads like other cryptography techniques.
The reason why it doesn't replace ZK, MPC, or FHE is because of the need to trust manufacturers for TEE. With cryptography you trust math, with TEE, you trust Intel or AMD. If there is a physical "backdoor" or a hardware bug, the privacy can be broken.
Other techniques
Stealth addresses — one-time address for receiving funds (avoid getting tracked)
Ring signature — combines your deposit with others to make it harder to track (e.g. Monero 16 rings)
Garbled circuits — the original 2-party version of MPC
Merkle Tree — summarize millions of pieces of data into a tree. You can prove your “leaf” (your deposit) is part of the “tree” (the pool) using a ZK-proof without showing which specific leaf is yours (Tornado Cash uses this)
Daml — Canton programming language with built-in privacy, designed for institutions. No extra encryption layers needed
Identity-based Encryption (IBE) — a way to send an encrypted message using a person’s real-world identity as their “public key,” [See example of this below in Fairblock]
zkTLS — prove APIs are legit. Useful for on‑chain settlement based on off‑chain APIs (e.g. banking data powering smart contracts). It is one of the most popular in 2026 in this category because it connects the Web2 world to Web3.
Example: Proving you have $5,000 in your real-world bank account to get a DeFi loan, but you don’t want to give the smart contract your login password.
zkTLS allows you to log into your bank, generate a ZK-proof that “this website says I have $5,000,” and send that proof to the blockchain.
Personal Observation
There are many cryptography/encryption camps (e.g. ZK, MPC, FHE, TEE, others). Each camp may prefer to use a combination of cryptography & encryption they like.
Just like there are thousands of ways to cook food, there are myriads of ways to deliver privacy solutions.
If we’re talking about delivering the most simple privacy use cases like private transfer or removing traces, then using ZK (or other techniques) might just be enough.
But If we’re talking about delivering the most complex privacy use cases for Defi, then a combination of more than 3+ of the techniques may be needed to keep the cost down while maintaining performance/speed.
In the end, the best privacy is the one that people use after all.
3. The Economy of Privacy
3.1 Supply of Privacy
Applications & Use cases
Applications, arguably one of the most important layers in privacy. Privacy technology is inherently difficult to understand, it’s often filled with jargon, and much of the tech is B2B instead of B2C.
Application layer changes this by bridging privacy tech with everyday people, enabling retail to experience & understand what on-chain privacy is like.
Because of how close applications are to the end users, most of the quantifiable privacy demand right now is happening within the application layer.
And the coolest thing is — the demand is being served by only a handful of applications.
Mixers
Private Transfer
Private Swap
Private Wallet
Private cross-chain messaging, lending/borrowing, yield farming
Mixers
Even though we have discussed how mixers work in the earlier section and even though everyday people may have negative connotation towards mixers (due to slew of headlines of scammers using mixers in the past),
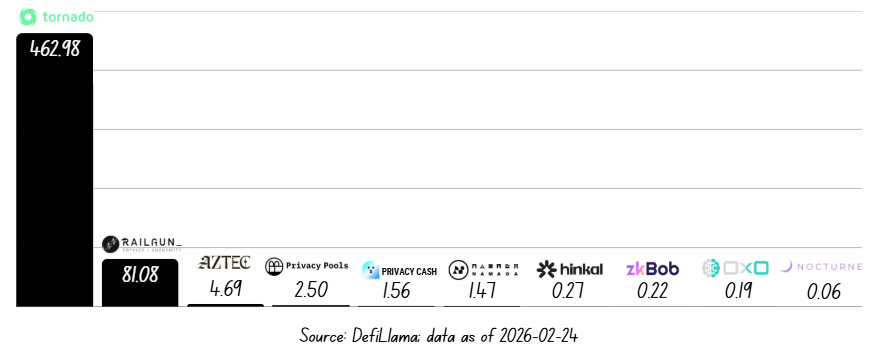
Mixers, Tornado Cash in particular, remains the most used privacy protocol in 2026. Tornado Cash made $5.6M in revenue in 2026. The protocol currently contributes >80% of the entire privacy TVL based on Defillama.
Source: DefiLlama; data as of 2026-02-24
Tornado Cash charges 0.3% on your deposit (which goes to $TORN incentives) + charges 0.05%-0.20% on withdrawal (paid to Relayers).
Relayers help users pay on-chain gas fees for the withdrawal & help users seed the new fresh wallet.
The main type of utility for Tornado Cash is breaking the link between sender & receiver (or old wallet & new wallet). Considering over $500M sits within the protocol, the demand for this particular use case is pretty high.
This is pretty wild because despite the high fees (30 bps in & 20 bps out) and despite knowing the risks associated with the protocol (potential blacklisted on centralized exchanges and defi protocols), users are still using Tornado Cash the most compared to other solutions.
In recent years, we’re seeing more mixers popping up, trying to capture users on different chains (e.g. Privacy Cash on Solana, Privacy Pools on EVM with Association Set Provider (ASP) feature that utilizes ZK to proof that the funds aren’t from illicit sources).
Tornado Cash remains the most used mixer because
1. First mover: battle-tested protocol since 2019
2. Brand: already garnered brand trust/known as the go-to mixer
3. Network effect: largest anonymity set (i.e. $2.5B in ETH was processed in 2025) the more funds in the mixers, the harder it is to track.
The network effect is really important here. Similar to AMM LP pool where small capital leads to high slippage, small capital in an anonymity pool leads to weak privacy.
Bootstrapping mixer is difficult because there's no Uniswap v3 or concentrated liquidity model to improve the efficiency of the anonymity set. This is why Tornado Cash has been dominating the segment.
Private Transfer
Considering that this is the most basic use case, there are many private transfer solutions out there. Each with their own pros and cons. I’ll highlight the mainstream options here
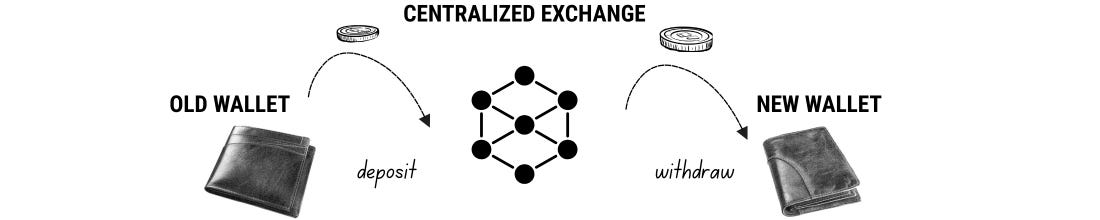
Private Transfer using Centralized Exchanges
Most popular option because of its ease-of-use
You can send any assets to other users on the exchange and people won’t be able to trace it. You can also seed a new wallet with your CEX account
Pros: Very easy to use. Optimal UI/UX, no need to go through hoops to access privacy
Cons: You give up your privacy up front (KYC when setting up the account). CEX sees your transactions. CEX can also freeze your funds/account. CEX retains a record linking your identity to that specific on-chain address for at least five years
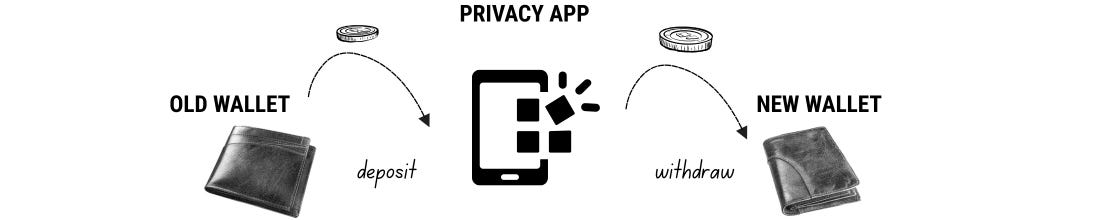
Private Transfer using Privacy Applications
Mixers remain the most used solution but there are other solutions out there that aim to navigate around the consequences of using mixers (blacklisted, offramping issues)
Multi-hop through 2 exchanges (i.e. Houdiniswap) or use escrow contracts to break links with node/relayer helping seed new wallets (i.e. Mirage)
Pros: Tend to have the best UI/UX, easiest to access right where you are (apps on EVM/Solana)
Cons: Negative connotation with mixers, fees tend to be high with privacy apps, alternative apps differ in trust assumptions and privacy guarantees
Private Transfer using Privacy L1s/Privacy-native Tokens
Utilize Monero, Zcash blockchain with their respective tokens as a medium of privacy exchange
Acquire the tokens on CEX, bridge them to respective chains, start transferring privately
Pros: Privacy integrated at protocol-level, everything is hidden, everything is like a dark tunnel
Cons: Often requires bridging from CEX. You might be able to use NEAR Intents to bridge ZEC. But for others, you’ll need a CEX account
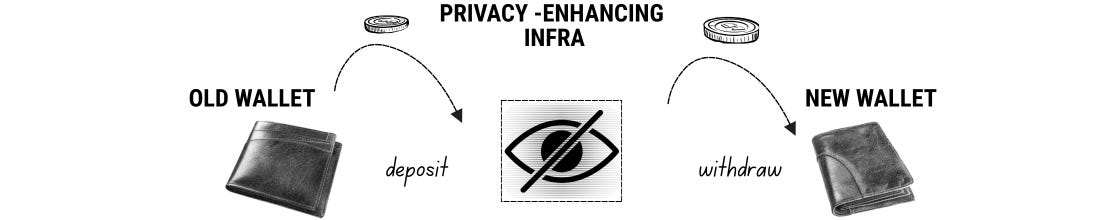
Private Transfer using Privacy-enhancing Infrastructure & L1s/L2s
There are 20+ protocols under this category, many of which are Privacy 2.0 infrastructure. Some accessible directly on Ethereum/Solana, some requires bridging to separate privacy L1s or Ethereum L2s
Often offer similar kinds of experience where you interact with a shielded pool (i.e. transferring privately within that pool) for complete privacy or confidentiality (only confidential info stays hidden)
Pros: Better UI/UX compared to privacy-native tokens. Depending on the infra, privacy is often integrated at protocol-level or smart contract-level. Compliance-ready features like selective disclosure, sanction/freeze list ensure compliance with KYC/AML rules & regulations
Cons: Face the same liquidity/anonymity set bootstrapping problem + same visibility problem like most solutions. Compliance-ready features can also be considered cons (barring you from accessing privacy or in worst case, getting traced & subpoenaed)
Visibility Problem
Most (or all) solutions often face the visibility problem.
When you’re depositing your funds into the shielded pool, other people see the deposit txn. While you’re in the pool, nothing can be seen. But when you withdraw, your funds can be seen again.
This is like people can watch you go into the tunnel and see you come out of the tunnel. You might be wearing different clothes and might come out a different person with different amounts of money — but pattern & timing analysis can be done (with varying degree of difficulties) to analyze and put two and two together. Thereby, identifying the old wallet to the new wallet.
Private DEX/Private Swap/Darkpool
Private DEX is considered a more complex use case that’s harder to pull off. This is because of the nature of blockchain — general blockchain are public by default, people can see the amount of the 2 tokens deposited into an AMM pool, they can track x * y = k, LPers can provide liquidity into the pool.
For a Private DEX, this is pretty different. If the orderflow, the liquidity, the tokens, the balances are hidden, then the question becomes how do we track these things, how do we rebalance the pool, how do orders get matched? You get the idea.
This is why darkpool or private trading use cases are being worked on first. How Darkpool generally works
Orders are matched off‑chain or in a special enclave/agent network.
Large orders get sliced, delayed, and internalized so size/side isn’t obvious.
The dark pool may internalize flow against its own books, or
Tap public DEXs/CEXs/LPs under the hood, while hiding the routing from the user.
Beyond hiding who traded, how much, at what exact time, and with which route, Darkpool also helps protect users from MEV attacks, achieving trades with better price. The top darkpool right now (based on my understanding) is Renegade on Arbitrum.
When it comes to a Private DEX with private pool state & DEX logic, I don’t think there’s any that’s live right now.
But, when it comes to the most used Private DEX alternative. It’s Houdiniswap.
The protocol serves 2 functions — private swap + private cross-chain bridging. Houdiniswap works by routing your funds through two separate exchanges, breaking the link with the original wallet.
How it works
User initiate the swap
Funds get sent to a one-time address that belongs to Exchange 1
Exchange 1 swaps your asset into a random L1 token
Exchange 1 sends the L1 token to Exchange 2
Exchange 2 converts your token into your desired output token and send it to the receiving address that you specified
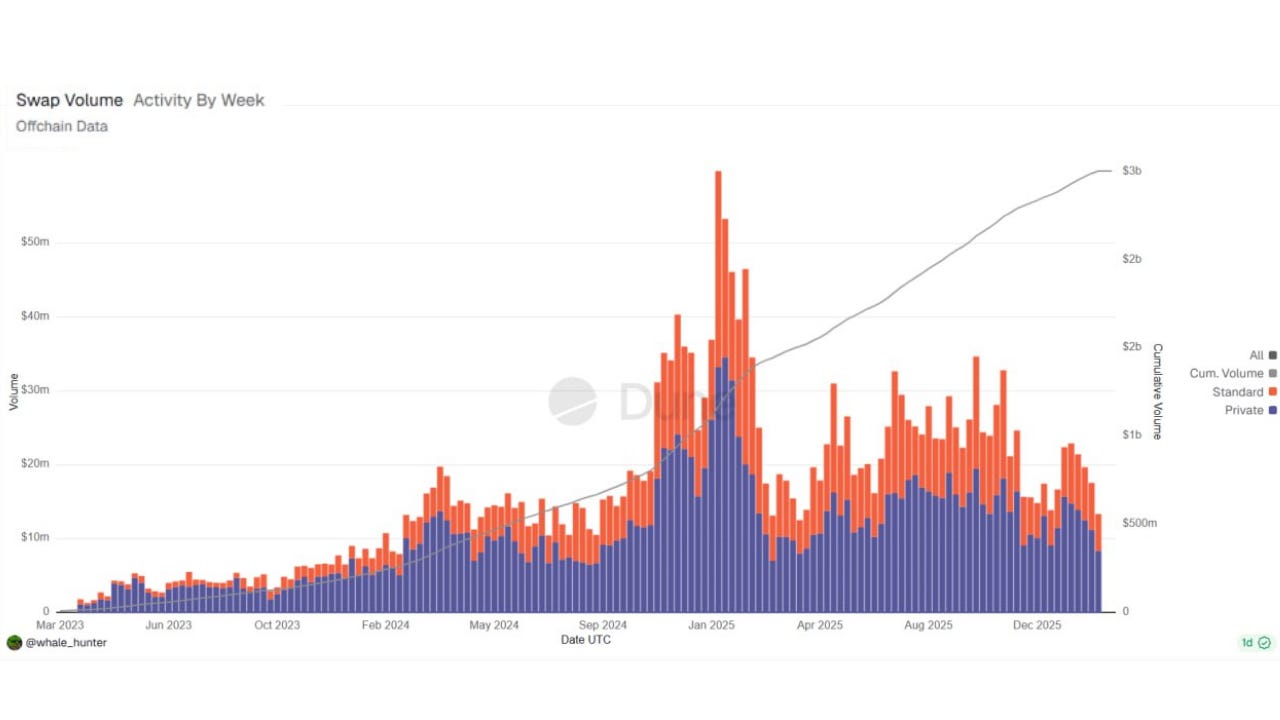
Source: Dune; data as of 2026-02-24
Houdini has done a cumulative volume of $2.5B. The protocol generated ~$4M in revenue in 2025 with cumulative revenue of $9M (based on @whale_hunter Dune Dashboard). The protocol charges 50 bps (0.5%) for private swaps.
This is even more wild because Tornado Cash only charges 30 bps (and that’s considered pretty high already). Demand for Houdini mainly comes from retail investors/traders/KOLs, people who are actively trading across multiple wallets and often get tracked by the community.
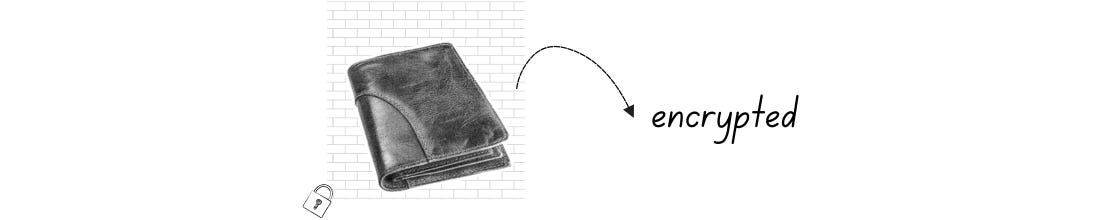
Private Wallet
If we’re talking about the most popular private wallet, we can’t not talk about wallets that have “CoinJoin” feature.
CoinJoin is a privacy-enhancing method for Bitcoin. It essentially joins Bitcoins (transactions) from multiple transactions together, forming 1 large transaction.
The transaction creates multiple new outputs of identical size (e.g., 5 users each receive exactly 0.1 BTC back). Because the outputs are identical, public eyes cannot tell which 0.1 BTC output belongs to which original user.
Wallet providers like Wasabi & Sparrow bake this feature into their wallets for ease-of-use but limitations remain as CEXes may flag or freeze funds originating from CoinJoin addresses due to AML requirements.
And while CoinJoin can obscure the trail, sophisticated tools continue to evolve to try and de-anonymize these transactions using statistical modeling so this is not a fool proof method.
Beyond Bitcoin privacy, players like Umbra on Solana are building private wallets designed for retail users to access private transfer & private swap experience inside the wallet itself. Umbra is leveraging Arcium MPC combined with its ZK technology to make this possible. This is currently on alpha/controlled rollout.
Private cross-chain messaging, lending/borrowing, yield farming
There are many projects building complex Defi use cases, I’ll highlight a few below (you can find more under the bonus section)
Private Cross-chain Messaging/Bridging
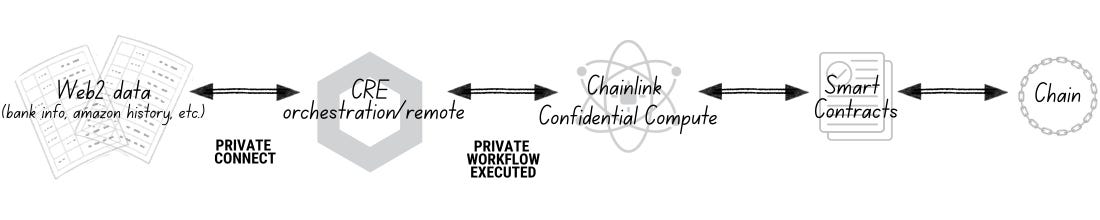
Chainlink
Chainlink is currently working on “Chainlink Confidential Compute”, unlocking private smart contracts on any blockchain using TEE + decentralized secret management (DKG) + powered by CRE.
“Chainlink Runtime Execution” (CRE) = an orchestration layer or a remote control that allows developers to write code that manages multiple blockchains and off-chain systems at once.
This enables private use cases for cross-chain messaging, transferring, processing of Web2/off-chain data into smart contracts (which means potential for undercollateralized lending/borrowing, private RWAs use cases as well). Chainlink Confidential Compute layer will be live later this year (2026).
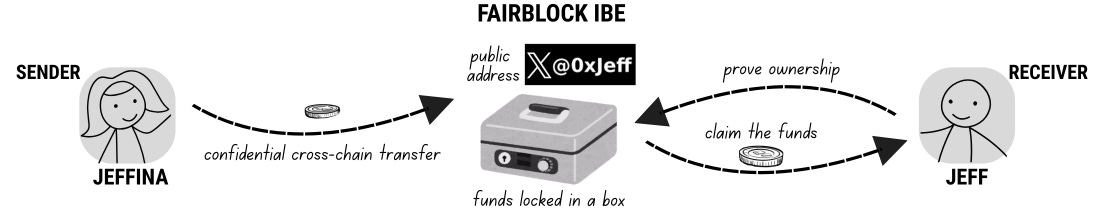
Fairblock
A privacy + cryptography layer for confidential stablecoins and confidential DeFi actions (transfers, auctions, swaps) that works across existing chains instead of forcing everyone onto a new privacy chain.
Fairblock utilizes a combination of ZK + HE + IBE and focuses on encrypted mempool (MEV prevention), and confidential cross-chain transfer use cases with stablecoins.
With IBE, sender can send confidential transfers on any chain using the identity of the receiver (email, Twitter handle) as a public address.
Sender sends funds
Funds locked inside an encrypted box, labeled with the identity of the receiver
Receiver prove they own that identity (e.g. ZKPs of Twitter handle)
Once proven, the validators generate a one-time Decryption Key for that specific identity. The receiver uses this key to unlock the box in the smart contract and tells the contract to “Send these funds to my existing wallet address.”
Fairblock is currently on testnet with mainnet expected soon in 2026.
Another interesting private cross-chain bridge is
Encrypt
Encrypt utilizes FHE + off-chain co-processors (with ZK + HE + TEE + MPC-style threshold decryption) to bridge assets privately across multiple blockchains without exposing wallet details, transaction amounts, or origins.
Users pay 0.35-0.5% to get fast, private execution (1-2 mins bridging). Liquidity is sourced via Near Intents network of solvers, and the tokens received from the network is encrypted with Encrypt homomorphic encryption (HE)
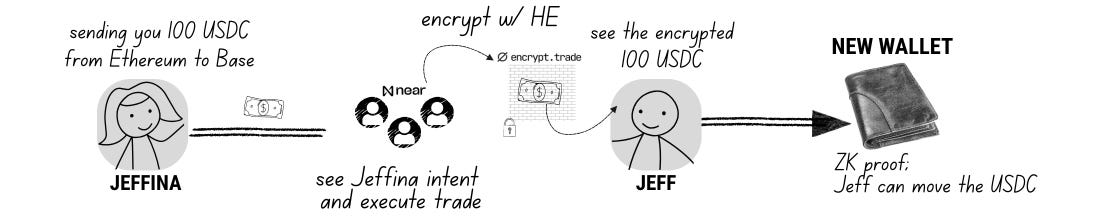
How private cross-chain bridging works (Example of Jeffina sending 100 USDC to Jeff from Ethereum to Base)
Jeffina signs a single message on Ethereum: “Send 100 USDC to Jeff’s private account on Base.”
A NEAR Intent Solver sees the request, takes Jeffina’s 100 USDC on Ethereum, and immediately uses its own funds to pay out 100 USDC on Base.
The Solver sends the 100 USDC into the Encrypt.trade Smart Contract on Base.
The contract “wraps” the money. It uses Homomorphic Encryption (HE) to add 100 USDC to Jeff’s private balance. On the blockchain, everyone sees the contract balance go up, but nobody sees that the 100 USDC belongs to Jeff.
Jeff opens his app and sees his private balance increased by 100. He inputs a new wallet address to withdraw.
Jeff’s app creates a ZKP which proves that “Jeff owns 100 USDC in this pool, but not disclosing which account is Jeff’s.”
The smart contract reads the proof, sees it is valid, and sends 100 USDC to Jeff’s new wallet.
Jeff has the money, but if an observer looks at the blockchain, the “trail” of breadcrumbs between Jeffina and Jeff is broken
Encrypt went live earlier this month (Feb 2026) and has done over $14M in volume during private beta.
Private Lending/Borrowing, and Yield farming
It’s extremely early for private permissionless lending/borrowing, and yield farming protocols. We’ll likely see private/confidential yield-bearing tokens first this year.
Since a lot of opportunity costs are lost during private transfer (i.e. money sit within anonymity set for days), introducing yield-bearing tokens as an option for medium of exchange is a good value proposition.
Players like Zenrock enable “shielded jitoSOL”, allowing users to earn yields on their SOL while staying private/confidential. This is already live.
Arcium works with Solana on C-SPL, confidential token standard on Solana. Once that’s live, Arcium general purpose MPC can enable confidential LSTs like jitoSOL (C-jitoSOL). Public eyes will be able to see a wallet holding C-SPL token but won’t be able to see the exact token balances. C-SPL will go live in Q1/2026.
Personal Observation
The most ideal privacy experience that builders are building towards is an end-to-end privacy experience. An experience where everything can stay confidential or anonymous while users perform everyday finance interactions (spending IRL, paying payroll, remittances, cross-border payments, invest in any assets, farm yields, lend & borrow, doing KYC) without sharing their sensitive information.
The truth is that we’re only at the starting point. Cryptography is certainly a crypto moat, it’s maturing pretty quickly but significant resources are required to scale the use cases as well as the adoption.
Privacy does not necessarily make money from Day 1. The protocols that make money now charge 25 - 50 bps which is ok but the goal would be to bring down the cost so privacy can be provided by default, without passing on large fees to everyday users.
3.2 Demand for Privacy
There are 4 main sources of demand for privacy such as retail users (traders/investors/HNW/crypto-natives), Crypto projects / DAOs, startups and enterprises (neobank, fintech, normal businesses) and Institutions.
Retail Users
Retail users are currently the group with highest demand. These are on-chain power users who often use popular privacy tools like Tornado Cash, Railgun, HoudiniSwap or interact with privacy L1s like Monero and Zcash.
KOLs and traders use these tools to seed new wallets and avoid getting tracked. Some also use it to seed new wallets so that they can also spend crypto IRL without getting traced.
These users often don’t mind paying 20-50 bps to execute a private txn because they’re used to paying 1-2% in a trade on pumpfun, or get sandwiched by MEV bots.
Main usage so far is private transfer, private payments, private cross-chain swaps
The demand from this group will continue to grow, as privacy becomes cheaper, more accessible, and easier to use.
Privacy preference: Very high on unlinkability + execution privacy. Less obsessed with perfect anonymity; for some, they’ll KYC if needed, as long as alpha and strategies aren’t visible. For others (Cypherpunk), maximal anonymity + confidentiality is needed, friction is ok in exchange for stronger guarantees.
Crypto Projects / DAOs
Crypto projects / DAOs are the group with the 2nd highest demand group but the demand is not as quantifiable as the 1st group.
Applications (Defi, AI, RWAs) are looking to integrate privacy as part of their tech in order to comply with rules & regulations, and sell to broader consumers (or institutions).
AI players opt for confidential compute and private inference to keep the prompt, the outputs, and the computation private
Defi & RWA integrate programmable privacy with selective disclosure, to ensure sensitive information (e.g. counterparty names, strategies, asset, balances, and terms) stay confidential
Arcium is likely the most successful privacy infrastructure player at consolidating the demand. There are more than 15+ projects currently building on Arcium tech stack.
From the POV of B2B users, crypto projects and DAOs tend to hold most of their runway on-chain. Being able to privately manage the treasury and pay employees, merchants, invoices, partners privately is key to preserving the confidentiality of the operation.
The demand from this group will likely grow the fastest, as privacy tailwinds continue to surge, and major privacy infra players (who raised hundreds of millions) continue to push for adoption.
Privacy preference: Strong demand for confidentiality (amounts, counterparties),
But also for clean auditability and compliance (view keys, selective disclosure); they don’t want Tornado‑style risk.
Startups and Enterprises
We can also segregate the demand within this group to 2 segments here
B2B consumers — businesses who want to pay their employees privately
B2B integrators — businesses who want to integrate privacy technology into their tech stack
The integrators are probably where most of this group’s demand is coming from. Neobanks, payment service providers, fintech startups that already have their distribution nailed down, and are looking to adopt blockchain rails & stablecoins to capture more margins/better efficiencies.
Emerging/developing countries will be the 1st place where adoption starts. From basic remittances, cross-border payments to automatic yields on idle capital, baking in defi as the default experience for users.
Privacy infrastructure projects tend to have a hard time capturing the demand from this group due to lack of enterprise/institutional sales expertise.
Privacy preference: Very high on regulatory acceptance and selective disclosure. They’ll sacrifice some anonymity for: clear governance over decryption, ability to show regulators/auditors what they need.
Institutions
Major institutions looking for privacy + blockchain solutions that can help make their processes more efficient (save costs, reduce time)
Institutions often take years to adopt a new piece of technology. This is why some institutions are starting with pilots and experiments
Canton has the highest number of pilots done with institutions
Test atomic settlements with 45+ institutions on tokenized securities, money market funds, and digital cash
DTCC tokenizing a subset of U.S. Treasuries custodied at the DTC for use as on-chain collateral (enable 24/7 liquidity, allowing firms to move Treasury collateral on weekends to meet margin calls in crypto or other markets)
Institutions want to use crypto without changing how they operate today. This means they want
Selective privacy
Transaction confidentiality (positions, balances, strategies)
Client confidentiality (who they transact with)
Protection of proprietary data
Clear auditability + regulatory access
Compliance embedded into the system
They don’t want manual compliance process nor after-the-fact reporting
They want compliance enforced at transaction level. This is
Identity attached to wallets (KYC/KYB tied to wallets)
Rules enforced automatically (transaction limits, sanctions checks)
Audit logs generated by default
Predictability and control
Institutions optimize for risk management, regulatory, and operational clarity (they gain to lose more than they gain to gain)
They want known counterparties, clear legal frameworks and deterministic/predictable settlements
The adoption will happen when crypto fits into institutions’ existing workflows
Privacy preference: Extremely high on all the above. Needs to cover complete end-to-end otherwise institutions won’t use it.
3.3 Privacy Ecosystem Map
If you’re interested in learning more about how each player maps out within the landscape, do let us know. We’ll likely do a deep dive on this in the next report.
4. Privacy by the Numbers
4.1 Key Figures & Traction of Privacy Projects
Total Market Capitalization (MC), Price Performance, Sentiment
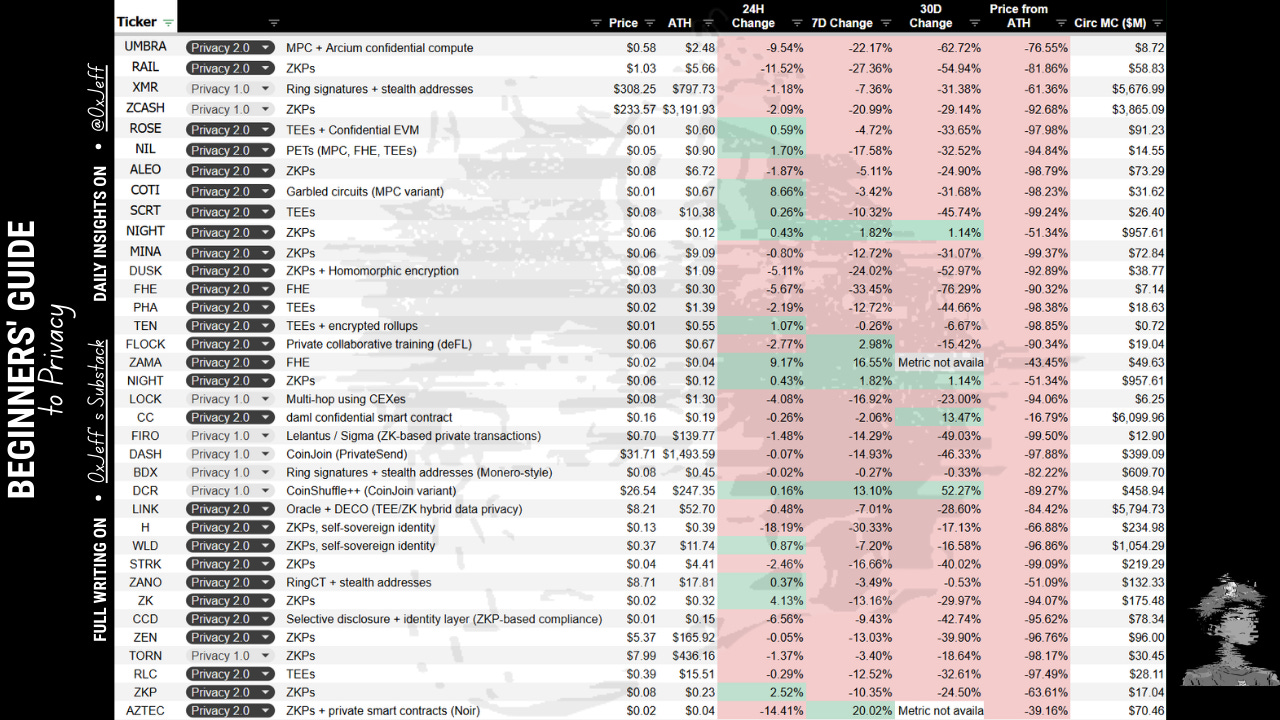
Total MC based on major privacy tokens tracked, is ~$28B. The MC has been shrinking together with the broader crypto market. None have shown any sign of outperformance except Canton ($CC)
Source: Artemis; data as of 2026-02-24
In Q4/2025, Zcash drove the surge in privacy tokens demand with its price action (went 14x from $50 to $700) thanks to privacy-focused communities + broader media coverage & key figures talking about the need for privacy.
Source: Coingecko; data as of 2026-02-24
The tailwind created a resurgence of interest in the privacy narrative, causing privacy alts to follow Zcash price action. However, the tailwind did not last very long.
Privacy (amongst other narrative) tumbled in price — new hyped launches like Zama, Aztec ended up launching far below its community round price (40-50%) despite hundreds of millions raised at ~$1B valuation from VCs.
Sentiment-wise, privacy is one of the top narratives in crypto right now. It is a part of almost every single conversation no matter the sector (stablecoins/payments, RWAs, AI, Defi, etc)
But with all the trends and conversations, positive sentiment does not seem to be reflected in the price of privacy tokens (at least for the time being). This is likely due to the lack of easy-to-understand narrative + lack of clear revenue generating businesses driven by privacy tech (beyond privacy 1.0 apps/chains).
So far, the only thing that people resonate with is the narrative of Zcash as “privacy Bitcoin” or “medium of private exchange”. Programmable Privacy/Privacy 2.0 is simply just too difficult to understand — too many jargons, and not enough people willing to deep dive and explain in a simple manner.
Well… hope this report changes things a bit (lol).
Total Value Locked (TVL)
Total TVL is $604M — the majority of TVL is captured by Tornado Cash (80% market share) and Railgun (~14% market share).
Privacy 1.0 projects tend to have very strong 1st mover advantage because if more people use the same privacy app, the more anonymity set there is, and the harder it is to trace the fund once it’s withdrawn.
Revenue
The top 3 privacy apps when it comes to annual revenue 2025
Tornado Cash $6M
Railgun $5M
Houdiniswap $4.3M
Source: Defillama, Dune Dashboard
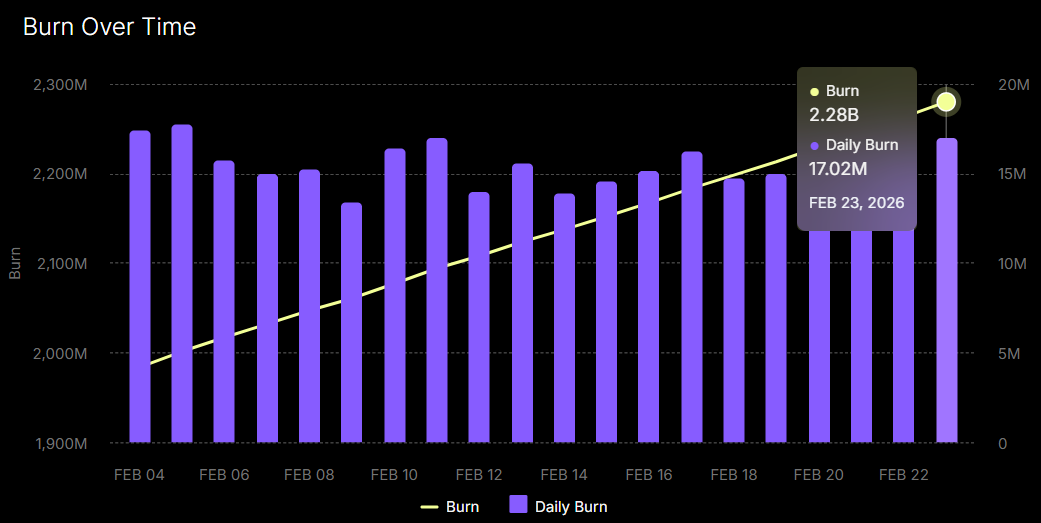
But if we look at the chain with embedded privacy that’s generating the most revenue right now, it’s Canton.
Source: Canton($CC); data as of 2026-02-24
Canton currently generates $2.69M in daily revenue. The Burn Over Time chart shows daily fee generated which goes towards buying back & burning $CC.
What contributes to such high revenue, you’re wondering?
Intraday Repo (Broadridge): Institutions use Canton to swap tokenized U.S. Treasuries for cash (stablecoins or tokenized deposits) and back again within the same day. This unlocks billions in liquidity that used to be “trapped” in 2-day settlement cycles.
Traditional repo markets usually settle in “T+1” or “T+2” days = cash and collateral are locked up for 48 hrs. On Canton, Broadridge uses smart contracts to execute “intraday” repos, loans that last only a few hours.
This allows banks to “rent” liquidity for exactly as long as they need it, then return it. By settling in minutes rather than days, it eliminates the need for massive “buffer” cash reserves, freeing up billions in capital for other uses.
24/7 Trading (Temple Digital): Institutions use Canton as the 1st private Central Limit Order Book for institutions. Sub-second execution, allowing institutions to trade crypto, stablecoins, tokenized equities, and commodities with the same speed as the NASDAQ but with 24/7 availability. And more case studies like these.
While retail privacy protocols are fighting for survival in a tightening regulatory landscape, Canton has quietly become the “privacy-as-a-service” layer for the world’s largest banks.
Goes to show the impact/the shift from a “niche tool for anonymity” to the “mandatory requirement for global finance.”
Funding Options
VCs
Since 2021, major VCs have invested billions into crypto privacy projects with a major focus on ZK technology and the emerging field of FHE.
Some of the top rounds include (but not limited to):
Matter Labs (zkSync) $458M raise led by a16z crypto, Blockchain Capital
StarkWare $287M raise led by Greenoaks, Coatue
Aleo $298M raise led by SoftBank, a16z crypto
Zama $150M raise led by Multicoin, Protocol Labs, Pantera
Aztec $119M raise led by a16z crypto, Paradigm
Most of the major rounds happened during 2022 & 2024, when appetite for pure infrastructure plays was high. Recent funding rounds have begun flowing into hybrid projects like Rain, which raised $250M in Jan 2026 to build compliant stablecoin infrastructure that includes privacy features for institutional users.
More investors are deploying into utility infrastructure or infrastructure that has clear use cases & clear demand primarily because large hundreds of millions rounds simply do not translate to PMF.
Most recent big names (but relatively small rounds) are Arcium ($14M) and Seismic ($17M)
VC funding into privacy projects tends to consolidate on high profile projects instead of smaller size projects. For single devs and smaller projects, best options in securing funding might just be grants, hackathons, and donations.
Grants, Hackathons
For early-stage developers and privacy researchers, non-dilutive funding remains the most viable path to sustaining operations without giving up equity or facing the immediate pressure of VC returns.
Ecosystem Grants
Major blockchain foundations have earmarked billions for ecosystem growth, with Privacy-Enhancing Technologies (PETs) and Zero-Knowledge (ZK) infrastructure being top-tier priorities in 2026.
Foundation-Led Programs:
Ethereum Foundation (ESP): up to $30k grants from small experiments to large infra research
Polygon Community Treasury: Deploying 1 billion POL over 10 years, specifically for ZK, DePIN, and infrastructure
Solana Foundation: Frequently awards grants between $5,000 and $250,000 for high-performance dApps and confidential infra
Privacy-Specific Grants:
Oasis Protocol Foundation: Dedicated funding for developers building on Sapphire ParaTime
iExec Ecosystem Fund: A 1,000,000 RLC fund specifically for projects integrating privacy stacks across AI, DeFi, RWA
Hackathons
Hackathons serve as high-intensity "sprints" where builders can secure initial capital and technical mentorship. In 2026, these events have shifted from general "building" to specialized tracks focused on production-ready privacy.
Solana Privacy Hack 2026: A global event ran early 2026, focused on ZKPs, private payments, compliant privacy tooling
ETHDenver 2026: Largest builder-driven event for Ethereum devs to ship private dApp prototypes (Feb 2026)
Zypherpunk Hackathon 2025: High-intensity developer sprints through a collab between Zcash & Starkware with $300,000+ prize pool. The momentum is carried into Re{define} Hackathon in 2026 for building privacy-preserving applications on Starknet
Devcon8: Taking place in Mumbai in November 2026, expected to be a major hub for L2 privacy and security.
Donations and Public Goods Funding
Privacy is increasingly viewed as a "public good," leading to the rise of community-funded donation models that bypass TradFi intermediaries.
Gitcoin & Quadratic Funding: Still a primary channel for decentralized projects to receive matched donations from the community based on wide supporter bases
Optimism Retroactive Public Goods Funding (RetroPGF): Rewards projects that have already provided value to the ecosystem, often funding essential open-source privacy tools
Direct Crypto Donations: Nonprofits & open-source projects now use gateways like Crypdonations to accept assets like Monero, stablecoins, and ETH directly from privacy advocates
Vitalik Buterin has become a key force in the privacy sector. He views privacy not as a luxury but as essential digital hygiene, a stance he backed in Jan 2026 by earmarking 16,384 ETH (~$45M) to a dedicated fund for privacy and security projects.
He recently provided significant funding to Shielded Labs for Zcash’s Crosslink security upgrade and split 256 ETH between Session and SimpleX Chat to advance metadata-free messaging.
Vitalik’s active use of protocols like Railgun serves as a high-profile endorsement of “Privacy Pools,” proving that sophisticated privacy can coexist with regulatory compliance.
What’s Next?
If you enjoy this report, do let us know.
If you want to dive deeper into privacy, feel free to subscribe here on Substack. We’ll be dropping deeper dives into the privacy industry, into the landscape, focusing on unique players in the space exclusively for our premium subscribers.
Want to Continue Reading?
Check out the articles below (if you haven’t yet)
What happens when a country runs an election with no privacy & no transparency (allegedly)
Institutions are coming. Why would this time be “different”?
Disclaimer: This article is provided solely for informational and educational purposes and may not be redistributed, reproduced, or modified. The insights presented reflect our own research and judgment and should not be interpreted as endorsements or recommendations. Nothing in this article constitutes financial, investment, or professional advice. Market conditions are inherently uncertain, and asset values can fluctuate significantly including the possibility that an investment may decline substantially or even lose its entire value. All investments involve risk. Any financial decisions you make after reading this article are entirely your own, and we do not accept liability for any losses or results that may follow. Readers should conduct their own independent research before making any financial decisions.
If you’re having any trouble with email delivery, payments, cancellations, un-subscriptions, or refunds, the best 1st stop is the Substack Help Center for Subscribers or Substack Support as they are great at sorting out those issues.
If your concern isn’t fully resolved or you need additional help regarding your subscription, we are here for you. Just reply to this email (if you’re reading it in your inbox) or send us a message through our Substack page.
Getting in touch with us helps ensure any issue is addressed promptly and that your access to our future activities and community channels continues smoothly.











Well done Jeff! Privacy is a non-negotiable for humans and this was a great read
Factor in my life dude. Appreciate the effort you put into this, learned a lot.This is an incredibly well structured guide